Blockchain-based KYC System
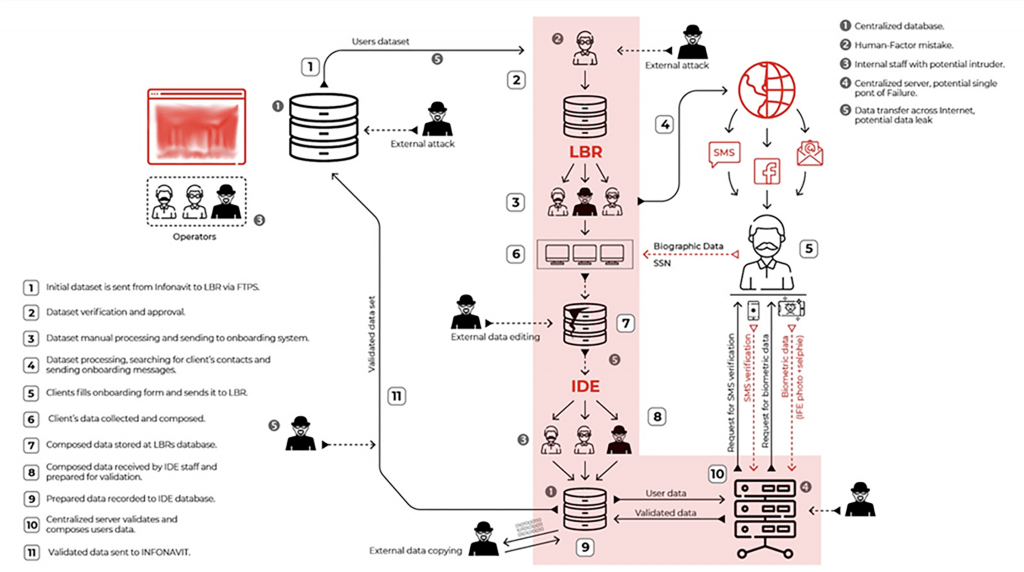
The Blockchain-based KYC System we built is a network of nodes with strict privacy rules and protection from copying or changing the information. The system validates the user’s data by biographical and biometrical information and sends it to the end owner (client). During data processing and validation, only the transaction information is stored in the distributed ledger without disclosing the user’s sensitive data. Blockchain is used to guarantee a transparent dataflow, collects validation results and real-time reports, ensures the automated workflow and permissioned access to data. IPFS is used to ensure the data storage security. Only the client can view or edit sensitive information. As all actions are tracked and logged in the blockchain, ML implementation is considered in future for fraud prevention or forecasting
Technology Stack
Hyperledger Fabric
GO

IPFS
Python
React Native
Product
The Know-Your-Customer system built on the basis of a distributed ledger technology allows verifying personal data in a database and returning the response to the requesting user. The database is implemented in the form of a private blockchain network with permissioned access and the request tracking function.
Business needs
This product is a solution for cases requiring user verification while strictly protecting their data from theft or other forms of compromising. All businesses handling sensitive data of their customers are facing the challenges of implementing sufficient protection and tracking. The distributed ledger technology is capable of providing the required degree of protection while covering the primary business needs.
Results
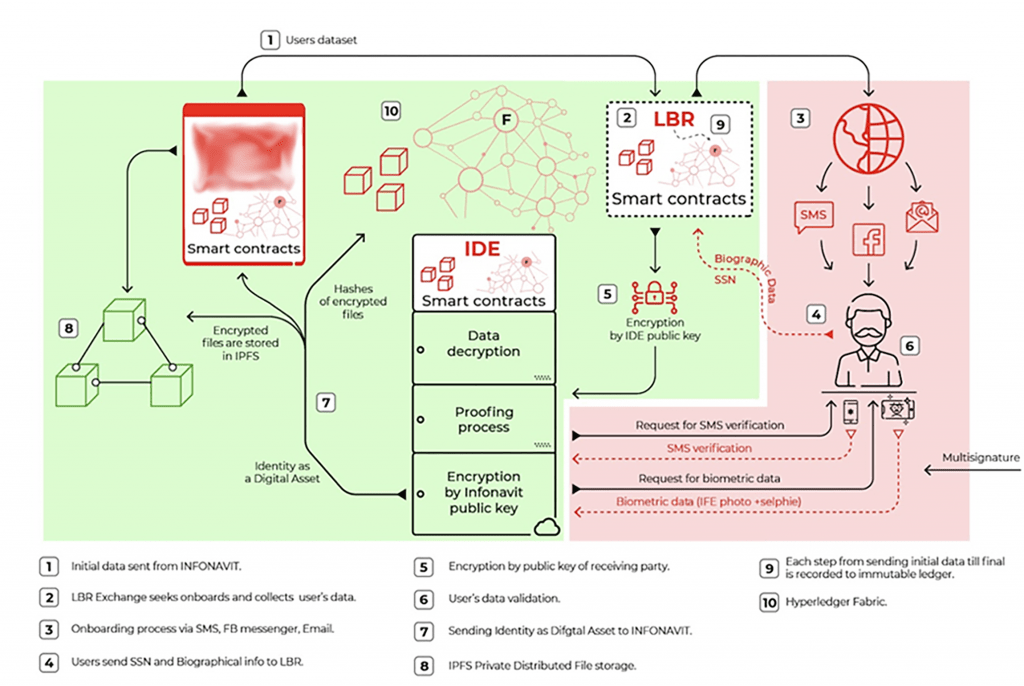
Adoriasoft built a secure distributed system for personal data storage with a permission policy allowing to assign different access levels to different executives and to monitor the use of the clients’ personal data. Within this project, we also created a web application serving as an entry point for the KYC system. Users’ data processing and verification became automated and faster due to the absence of the human factor and the related mistakes. All verification steps are recorded in an immutable ledger. The logging system is protected from edits and, therefore, guarantees transparent and trusted reporting. Thus, for any data request it is known who requested it, when the request was made, and what data was requested. Also, the logging system stores all actions performed to the users’ information.
